Ever heard of Emotet? And have you ever wondered why there are such dangerous and powerful digital attacks? Indeed, behind these malware attacks are huge and powerful structures, made up of multiple machines, running one or more bots … hence the name botnet.
The National Cybersecurity Center (CNCS) recently posted a social media warning about the world’s most dangerous malware, Emotet.
Emotet impacted 25% of Portuguese organizations
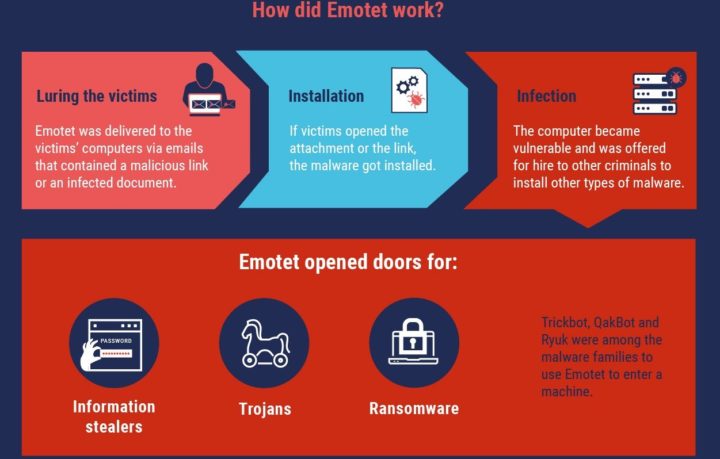
Emotet is a type of malware originally developed as a banking trojan with the aim of stealing financial data, but its evolution has made it a major threat to users around the world.
CNCS has once again recorded an increase in the sending of emails containing malicious code (malware) from the Emotet family. After 4 months, a new vacancy is registered.
These emails are, or pretend to be, sent from addresses known to recipients and may appear as a response to previous conversations. This malicious code is characterized by sending hidden emails to victims' contact lists.
We recommend more attention to received attachments and malicious links present in the email. Note that the use of password-protected compressed folders (zip files) (usually present in the body of the e-mail), containing the malicious files, is prevalent.
Be wary of messages with a sense of urgency that ask you to download files or click links.
The Emotet trojan topped the threat index, with a global impact of 7% of organizations, following the spread of a spam campaign that, during the 2020 holiday period, affected more than 100,000 users per day . In Portugal, the Trojan impacted 25% of Portuguese organizations.
Emotet has evolved and served as a vehicle for the spread of other malware and malicious campaigns. It used various evasion methods and techniques to maintain its persistence and avoid detection. Furthermore, it could be spread via phishing spam emails containing malicious attachments or links.